Review Study of Navigation Systems for Indian Regional Navigation Satellite System (IRNSS)

This review study examines the navigation capabilities and applications of the Indian Regional Navigation Satellite System (IRNSS). It analyzes system architecture, signal structure, and performance in providing accurate positioning and timing services across India and surrounding regions. The study highlights IRNSS applications in transportation, aviation, maritime navigation, disaster management, and defense. By offering regional autonomy […]
Map Matching Approach for Current Location Tracking on Road Network

This study presents a map matching approach for accurately tracking current vehicle location on road networks. By aligning raw GPS data with digital road maps, the method minimizes positioning errors caused by signal noise or urban obstructions. The approach improves navigation accuracy, route consistency, and real-time tracking reliability. It supports intelligent transportation systems, traffic monitoring, […]
IoT for Fight Against COVID-19

This study explores how Internet of Things (IoT) technologies support healthcare systems in combating COVID-19. By integrating wearable sensors, mobile health applications, and connected medical devices, IoT enables real-time monitoring, early detection, and efficient patient management. Automated systems such as drones and smart sanitization tools reduce human contact and improve response speed. These IoT-driven solutions […]
Alert-Based Drowsiness Detection Using Machine Learning

This research presents an alert-based drowsiness detection system that uses machine learning to analyze driver behavior in real time. By monitoring facial expressions, eye movement, and head position, the system identifies early signs of fatigue and triggers timely alerts. The approach improves driving safety by reducing the risk of accidents caused by drowsiness. The study […]
Deep Learning in Object-Oriented Software Engineering: A Case Study of Stability

This study investigates the application of deep learning techniques in object-oriented software engineering to evaluate system stability. By analyzing object-oriented metrics, class relationships, and design structures, the model identifies patterns that influence long-term software reliability. The case study demonstrates how deep learning can improve stability prediction compared to traditional methods. These insights help developers detect […]
Data Dissemination in Vehicular Edge Network

This study focuses on efficient data dissemination mechanisms within vehicular edge networks to support real-time communication among vehicles and infrastructure. By processing data closer to the network edge, the system reduces latency and improves responsiveness for safety-critical and traffic-related applications. The research examines communication strategies that enhance data reliability, scalability, and bandwidth utilization. These approaches […]
Feedback Linearization and Self-Tuning PD Fuzzy Controller for Wheeled Mobile Robot
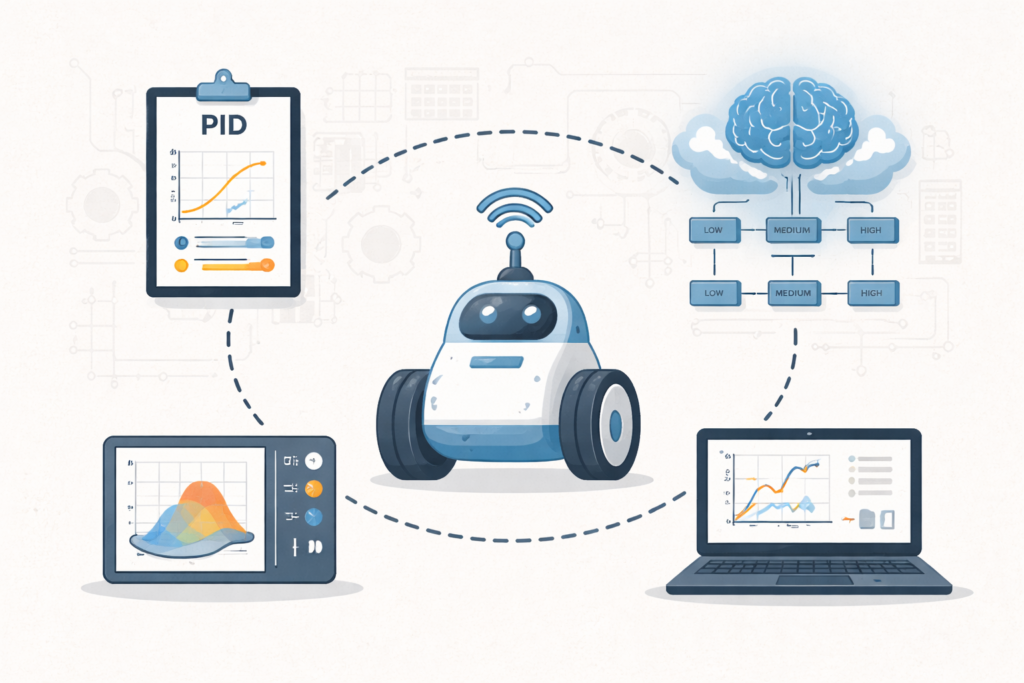
This research presents an intelligent control approach for wheeled mobile robots using feedback linearization combined with a self-tuning PD fuzzy controller. The method dynamically adjusts control parameters to handle nonlinearities and uncertainties in robot motion. By integrating fuzzy logic with conventional PD control, the system improves tracking accuracy, stability, and responsiveness. The proposed approach enhances […]
Critical Review: Fog Computing Dimensions for Data Security Features in Cloud-Based Applications

This review critically examines the role of fog computing in enhancing data security for cloud-based applications. By distributing computation closer to end devices, fog architecture improves access control, reduces latency, and limits data exposure to security threats. The study analyzes key security dimensions, including authentication, encryption, and intrusion detection, within fog-enabled systems. These insights highlight […]
Leveraging Cloud Technology for Enhanced Online Examination System
This study explores how cloud technology can enhance online examination systems by enabling secure, scalable, and easily accessible testing environments. With cloud-based storage and real-time synchronization, exams can be administered and monitored across multiple devices while maintaining consistent performance. The approach improves data management, reduces system failures, and ensures reliable exam delivery. Cloud integration also […]
A Comprehensive Study on Steganography and Text-to-Image Encryption Using RGB Substitution Techniques for Cybersecurity

This study explores the use of RGB substitution techniques to perform steganography and text-to-image encryption for cybersecurity applications. By embedding text within image color channels, the method conceals sensitive information while maintaining visual integrity. The research analyzes encryption strength, data-hiding capacity, and resilience against attacks. These techniques enhance secure communication, reduce detection risks, and support […]